Category: Security
-
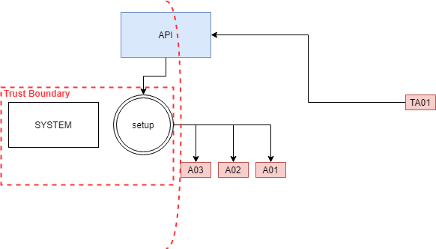
SCCM Tampering with deployment boundaries for EoP
Read more: SCCM Tampering with deployment boundaries for EoPIn a large-scale environment, software deployment automation provides efficiency for employees and the IT departments. Moreover, It solves existing challenges but brings new ones. These challenges require adaptation from the…
-
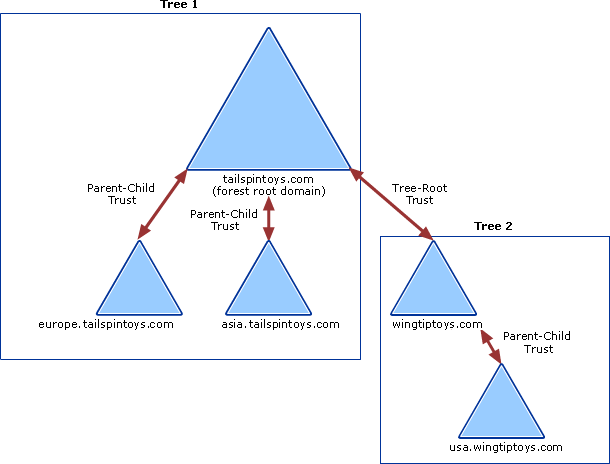
Jump between domains – Enterprise Admins Golden Ticket
Read more: Jump between domains – Enterprise Admins Golden TicketHow to take over all the domains. But let’s add a quick recap first. To build an active directory domain, you start with a root domain, for example, UNIXAWY.CORP, which…
-
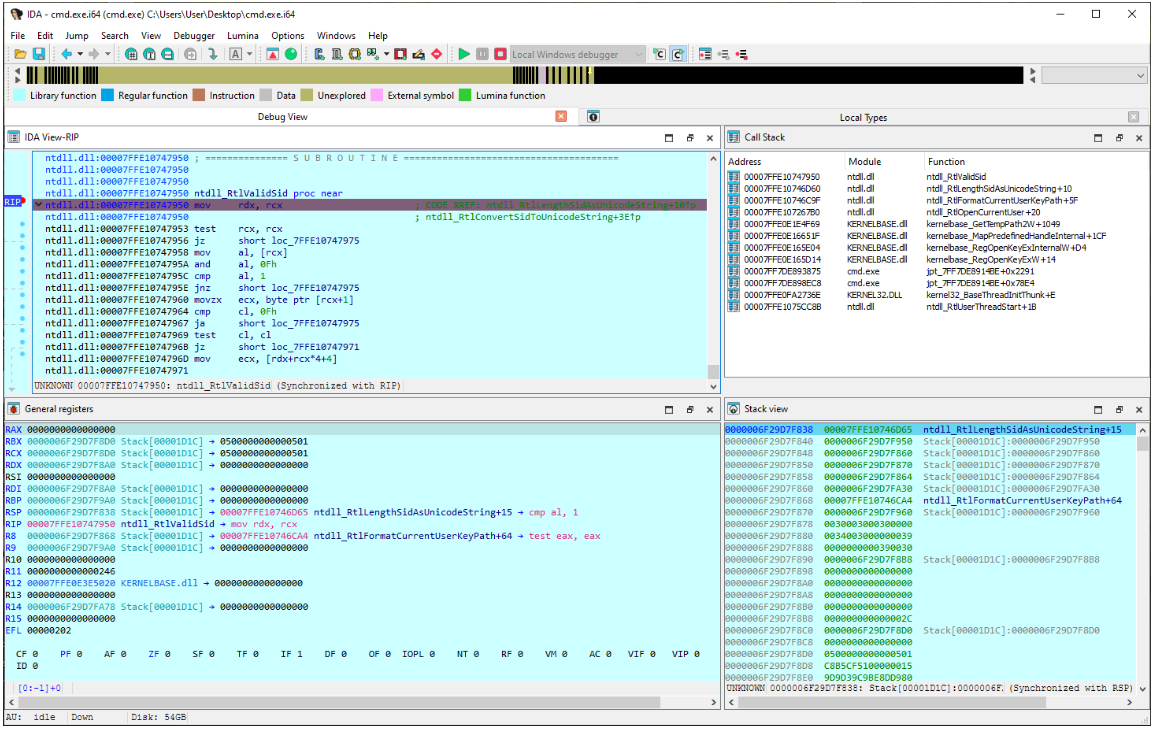
IDA Debugger: you don’t have the necessary privileges.
Read more: IDA Debugger: you don’t have the necessary privileges.during reverse engineering session, I encountered error from IDA saying “The debugger could not attach to the selected process. This can perhaps indicate the process was just terminated, or that…
-
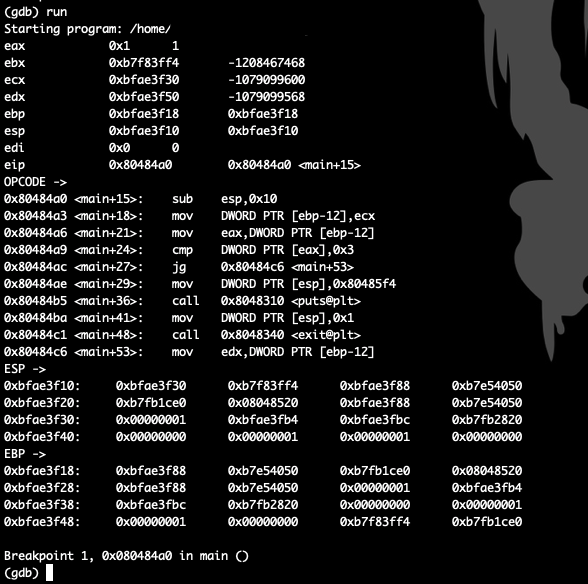
GDB hook .gdbinit
Read more: GDB hook .gdbinitGDB hook that helps without third-party apps set disassembly-flavor intel define hook-stop info register eax info register ebx info register ecx info register edx info register ebp info register esp…
-
audit keystrokes with pam
Read more: audit keystrokes with pamThe pam_tty_audit PAM module is used to enable or disable TTY auditing. By default, the kernel does not audit input on any TTY this module is part of auditd and…
-
Protect Boot & Single user mode
Read more: Protect Boot & Single user modeas a physical security is the main factor in our security perspective we all need to protect unauthorised access to our Linux box after we protect bios and we all know…
-
Secure/Lock accounts with PAM tally2
Read more: Secure/Lock accounts with PAM tally2pam_tally2 is a PAM module to allow interaction in users interfaces on numbers of failed login attempt it can reset count on success, can deny access if too many attempts fail. this…
-
password policy with pam_cracklib
Read more: password policy with pam_cracklibcracklib pam module is a method to check the password against dictionary list and gives you availability to check the strength of the password and set rules to identify the…
-
Pluggable Authentication Modules
Read more: Pluggable Authentication ModulesLinux comes with Pam Modules to help you to interact with the running services in hardening way and custom the security of the service as you need. PAM is extra…
-
AIDE : Intrusion Detection Environment
Read more: AIDE : Intrusion Detection Environmentthis article about Intrusion Detection for file system changes like modification changing owner extra, for critical files or directories in our environment we using a software called AIDE Advanced Intrusion…