
Hi, I’m Ahmad Mahfouz
Staff Cybersecurity Engineer @ ServiceNow | Strategic Leader in Vulnerability Management & Offensive Operations | Ex-SWIFT | GXPN, OSCE, GSTRT | Critical Infrastructure Expert
I am passionate about building resilient security cultures and scaling defense in the world’s most high-pressure environments.
Latest Articles
Thoughts, tutorials, and insights on building a personal brand online.
-
· 5 min read
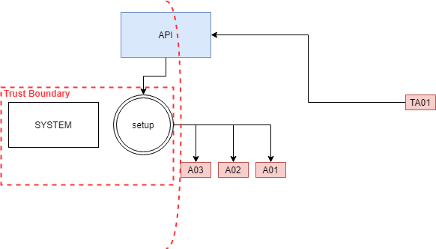
SCCM Tampering with deployment boundaries for EoP
Read more →: SCCM Tampering with deployment boundaries for EoPIn a large-scale environment, software deployment automation provides efficiency for employees and the IT departments. Moreover, It solves existing challenges but brings new ones. These…
-
· 5 min read
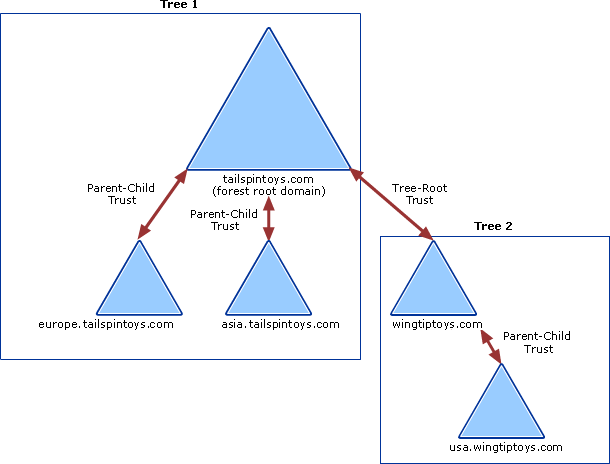
Jump between domains – Enterprise Admins Golden Ticket
Read more →: Jump between domains – Enterprise Admins Golden TicketHow to take over all the domains. But let’s add a quick recap first. To build an active directory domain, you start with a root…
-
· 5 min read
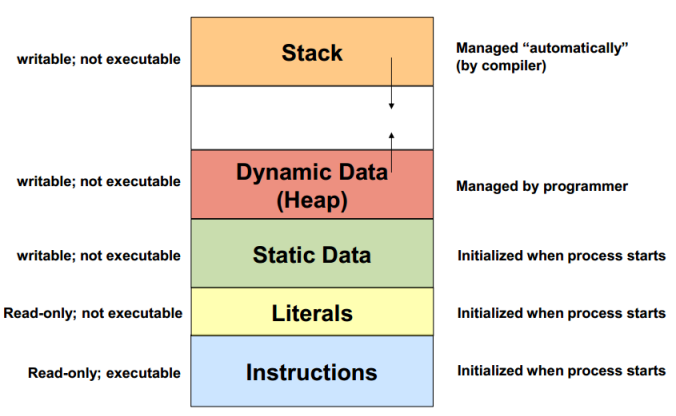
Heap Memory
Read more →: Heap MemoryHeap Memory, it starts from lower address and increases to higher address malloc malloc(size) allocate memory, return a pointer realloc(pointer, size) resize currently allocated memory…
-
· 5 min read
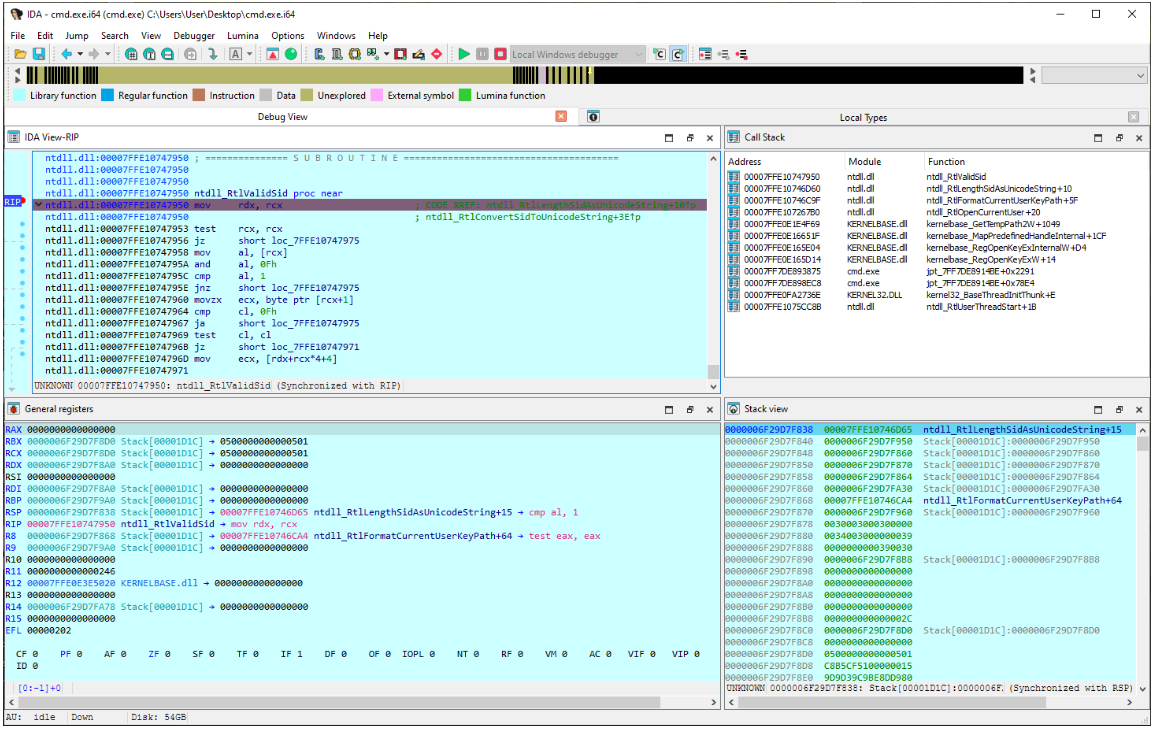
IDA Debugger: you don’t have the necessary privileges.
Read more →: IDA Debugger: you don’t have the necessary privileges.during reverse engineering session, I encountered error from IDA saying “The debugger could not attach to the selected process. This can perhaps indicate the process…
-
· 5 min read
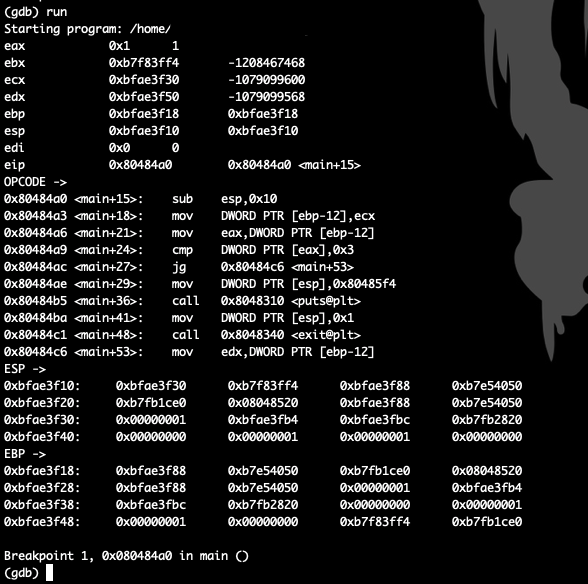
GDB hook .gdbinit
Read more →: GDB hook .gdbinitGDB hook that helps without third-party apps set disassembly-flavor intel define hook-stop info register eax info register ebx info register ecx info register edx info…
-
· 5 min read
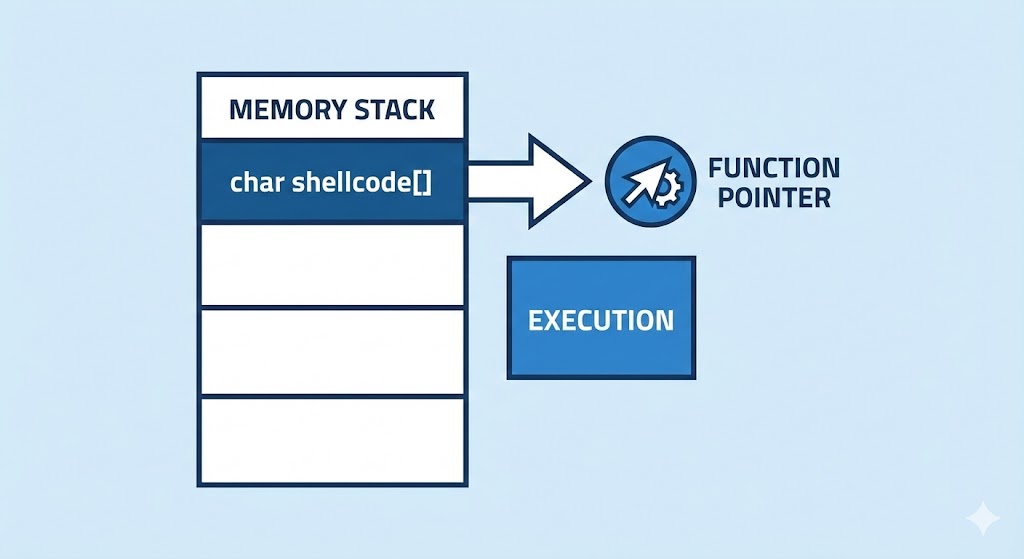
Shellcode validation via C pointer
Read more →: Shellcode validation via C pointerC snippet to test the shellcode replace your shellcode with your custom payload char shellcode[] = “\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc\xcc”; int main(int argc, char **argv){ int (*target)();…