Category: tech
-
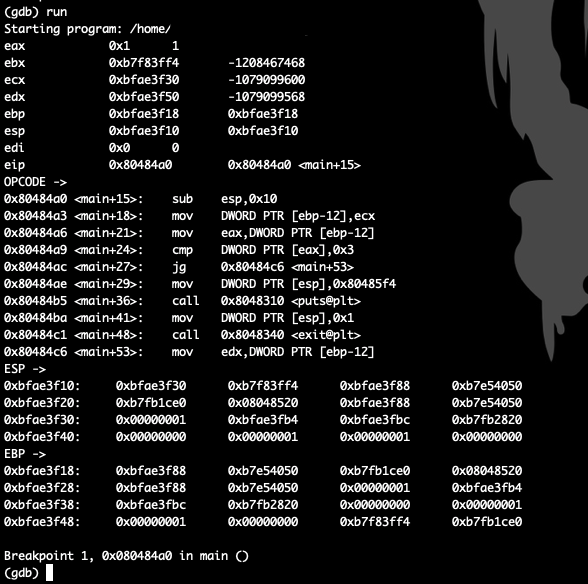
GDB hook .gdbinit
Read more: GDB hook .gdbinitGDB hook that helps without third-party apps set disassembly-flavor intel define hook-stop info register eax info register ebx info register ecx info register edx info register ebp info register esp…
-
Run MySQL Cluster Multi Masters For High Availability
Read more: Run MySQL Cluster Multi Masters For High AvailabilityHello Folks, it’s has been a while I didn’t write new articles, it’s has been a while I didn’t write new articles, so time to give back to the community,…
-
Linux Performance Co-Pilot with WebUI
Read more: Linux Performance Co-Pilot with WebUIPerformance Co-Pilot allow sysadmins to collect and measure data from various systems, it comes in RPM packages for Red Hat 6 to 7 website http://pcp.io/ installing Performance CO-Pilot yum -y install…
-
Facebook Mass Invite to Like script
Read more: Facebook Mass Invite to Like scripttoday I wrote a script to help in sending an invitation to like your page this happens when you promote a post for your audience and they interact with your…
-
Docker Persistent Storage for MySQL Server and SELinux
Read more: Docker Persistent Storage for MySQL Server and SELinuxhello everyone today we will make MySQL Docker Container with Shared Storage first let’s pull latest MySQL version of docker docker pull mysql after we did download the latest image this…
-
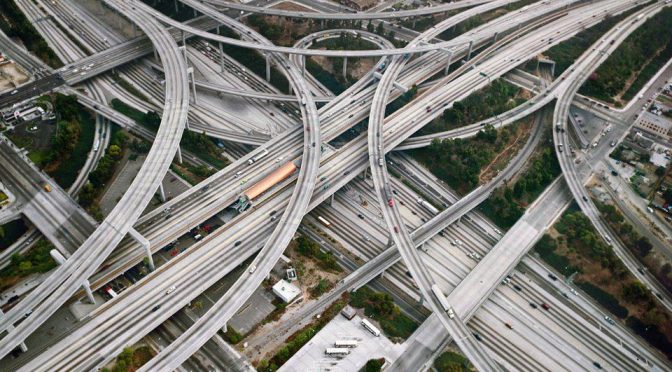
IPtables PREROUTING, POSTROUTING for mixed interfaces via DNAT & SNAT
Read more: IPtables PREROUTING, POSTROUTING for mixed interfaces via DNAT & SNATTraffic Forwarding with iptables Let’s get straight to the point. We are looking at two specific networking scenarios: Simple Traffic Forwarding: Routing traffic from a specific Source IP through our…
-
Protect Boot & Single user mode
Read more: Protect Boot & Single user modeas a physical security is the main factor in our security perspective we all need to protect unauthorised access to our Linux box after we protect bios and we all know…
-
SSH Tunnelling
Read more: SSH Tunnellingthe most famous method is using D parameter in ssh connection to bind a port local in your machine and this port tunnel back to our remote box to send…
-
Secure/Lock accounts with PAM tally2
Read more: Secure/Lock accounts with PAM tally2pam_tally2 is a PAM module to allow interaction in users interfaces on numbers of failed login attempt it can reset count on success, can deny access if too many attempts fail. this…
-
password policy with pam_cracklib
Read more: password policy with pam_cracklibcracklib pam module is a method to check the password against dictionary list and gives you availability to check the strength of the password and set rules to identify the…