Category: exploit-dev
-
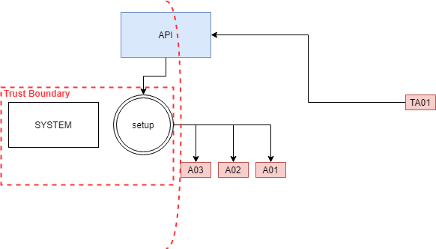
SCCM Tampering with deployment boundaries for EoP
Read more: SCCM Tampering with deployment boundaries for EoPIn a large-scale environment, software deployment automation provides efficiency for employees and the IT departments. Moreover, It solves existing challenges but brings new ones. These challenges require adaptation from the…
-
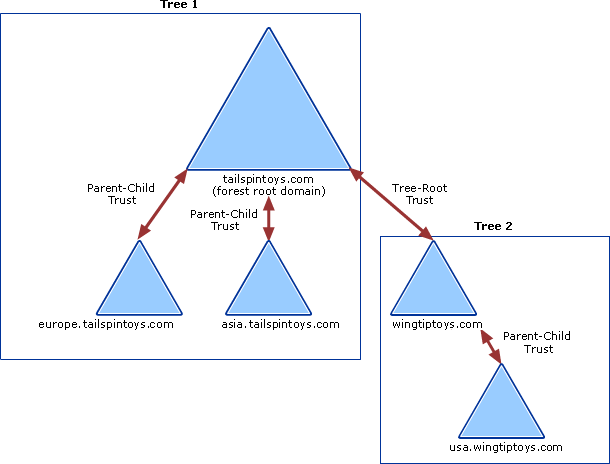
Jump between domains – Enterprise Admins Golden Ticket
Read more: Jump between domains – Enterprise Admins Golden TicketHow to take over all the domains. But let’s add a quick recap first. To build an active directory domain, you start with a root domain, for example, UNIXAWY.CORP, which…
-
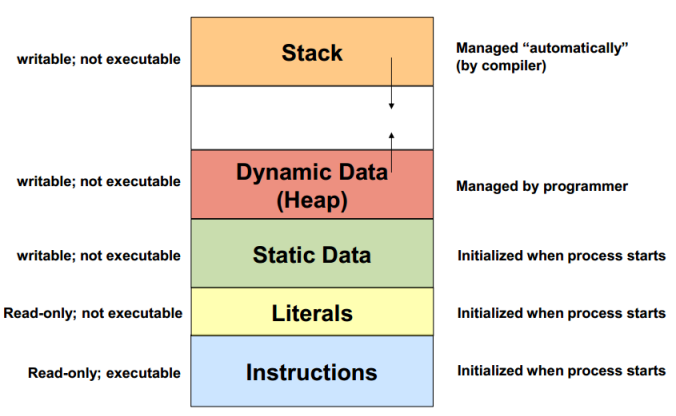
Heap Memory
Read more: Heap MemoryHeap Memory, it starts from lower address and increases to higher address malloc malloc(size) allocate memory, return a pointer realloc(pointer, size) resize currently allocated memory for bigger or lower by…
-
Google Drive Information Leak
Read more: Google Drive Information LeakGoogle Drive & Gmail attachments Leak This part of Google bounty program [IDOR] exploit to allow the attacker to leak your Google Drive files and this mean attacker could leak…
-
MetaSploit Payload to Executable EXE
Read more: MetaSploit Payload to Executable EXE# msfvenom No options Usage: /opt/metasploit/apps/pro/msf3/msfvenom [options] <var=val> Options: -p, –payload <payload> Payload to use. Specify a ‘-‘ or stdin to use custom payloads -l, –list [module_type] List a module…
-
SMASH THE STACK LEVEL6
Read more: SMASH THE STACK LEVEL6Smash The Stack Level 6 level6@io:/levels$ ./level06 a b Hi a this app take 2 argument 1 – username 2- password it takes it then say hi also, it checks…
-
Get Environment Variable memory Address
Read more: Get Environment Variable memory Addresssome time u put the shellcode inside the environment and u will need the address of it to build ur payload here is a simple C code to get the…
-
SMASH THE STACK LEVEL 5
Read more: SMASH THE STACK LEVEL 5still smashing 😀 level5@io:/levels$ ./level05 level5@io:/levels$ ./level05 a a level5@io:/levels$ echo one 😀 let’s see the source code level5@io:/levels$ cat level05.c #include #include int main(int argc, char **argv) { char…
-
SMASH THE STACK LEVEL4
Read more: SMASH THE STACK LEVEL4level 4 😀 level4@io:~$ cd /levels/ level4@io:/levels$ ./level04 Welcome level5 level4@io:/levels$ ./level04 d Welcome level5 level4@io:/levels$ ./level04 $(python -c “print ‘A’ * 1024”) Welcome level5 so i will read the…
-
underc0de 3 WalkThrough
Read more: underc0de 3 WalkThroughloaded the virtual machine and run netdiscover to get the machine IP oot@n1x:~# netdiscover Currently scanning: 192.168.39.0/16 | Screen View: Unique Hosts 4 Captured ARP Req/Rep packets, from 4 hosts.…